The bxp Infrastructure
From All n One's bxp software Wixi
Contents
1 Overview
The bxp software (bxp) infrastructure is a multi-tier design to delivery high availability with our own private infrastructure within Amazon Web Services. Bxp_software_in_AWS_Cloud_Services
bxp is built on a WIMA stack (Windows, IIS, MySQL, ASP).
For more information on stacks | Stack Information
2 Physical Infrastructure
bxp software is hosted from the AWS data facility hosted within Ireland (eu-west-1). This Data center and the off-site disaster recovery site for bxp are ISO27001 Certified. (https://d1.awsstatic.com/certifications/iso_27001_global_certification.pdf)
3 Secure Design
AWS performs initial environmental and geographic assessments. Data center locations are carefully selected to mitigate environmental risks, such as flooding, extreme weather, and seismic activity. AWS Availability Zones are built to be independent and physically separated from one another.
4 Redundancy
Data centers are designed to anticipate and tolerate failure while maintaining service levels. In case of failure, automated processes move traffic away from the affected area. Core applications are deployed to an N+1 standard, so that in the event of a data center failure, there is sufficient capacity to enable traffic to be load-balanced to the remaining sites
bxp has disaster recovery support contract with AWS to move bxp software's operations to our redundant offsite infrastructure hosted in AWS' France facility (eu-west-3). A simulation of this process is run annually.
AWS provide numerous high level interconnects to provide redundant Internet connectivity.
At no point in communication of data does the data leave an encrypted state, even data at rest.
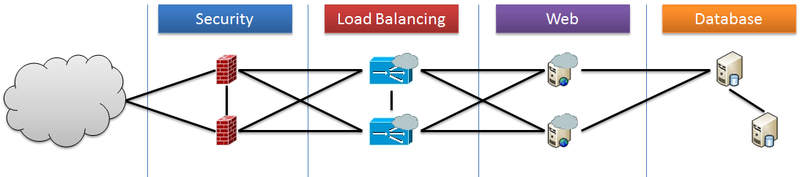
- Security
- Load Balancing
- Web
- Database
4.1 Firewall Security
The high available firewalls are implemented using AWS' network firewalls. This is a managed service with AWS. The Network Firewall includes features that provide protections from common network threats. AWS Network Firewall’s stateful firewall can incorporate context from traffic flows, like tracking connections and protocol identification, to enforce policies such as preventing bxp's metwork from accessing domains using an unauthorized protocol. AWS Network Firewall’s intrusion prevention system (IPS) provides active traffic flow inspection so bxp can identify and block vulnerability exploits using signature-based detection. AWS Network Firewall also offers web filtering that can stop traffic to known bad URLs and monitor fully qualified domain names. For more information visit (https://aws.amazon.com/network-firewall/?whats-new-cards.sort-by=item.additionalFields.postDateTime&whats-new-cards.sort-order=desc)
4.2 Load Balancing
The load balancers are implemented using highly available AWS Application/Network Load balancers. This service allows us to protect our encrypted HTTPS connections ensuring the usage of strong TLS1.2 and cipher suite technology. For more information (https://aws.amazon.com/elasticloadbalancing/)
4.3 Server Monitoring
Live 24/7 monitoring from our AWS support team, with alerts and calls to bxp team if required. An ISMS for our servers is monitored by Datadog HQ (https://www.datadoghq.com/product/)
4.4 Web
The web servers are implemented using Windows Server on a virtualised basis.
4.5 Database
The web servers are implemented using Windows Server on a virtualised basis.
5 Logical Infrastructure
5.1 Data Segregation
Within this common infrastructure data segregation is key. Though the solution uses a common infrastructure, logically the data is completely segregated. This segregation occurs at a web and database level.
This area is often referred to as multi-tenancy or multitenancy. Multi-tenancy is an architecture in which a single instance of a software application serves multiple customers. Each customer is called a tenant. In the case of bxp, the software does share common functionality, but each system is a separate instance, as is each separate database. Wikipedia - Multitenancy
5.2 Web segregation
Each client is given their own unique folder within the web structure. Our demo system has the link https://ww3.allnone.ie/client/client_demo/main/login.asp. The client_demo part segregates the web file infrastructure uniquely. Each client has their own folder structure which is independent of all other systems.
A set group of unique identifiers hard coded at the web layer ensures that database connections are only possible to one client database at a time. This is encoded into all operational pages of the solution.
5.3 Database segregation
Each client has their own separate database. Each database begins with a common suite of tables making up the database structure independent of all other databases. As content is added each database grows according to the specific client needs.
Each database is combined with the web segregation to provide full and unique audit trails for all interactions with that database. This is part of the design of the bxp solution.
Backups of databases are unique to each client and encrypted separately. Bxp_Backups
Strong security and operational procedure controls ensure this segregation is maintained by all personnel with access. All interactions are auditable.
5.4 Server Patching Process
Servers are checked for patches and updates daily. These updates are downloaded and installed on Thursday evenings as part of bxp' scheduled maintenance hours 22:30-00:30. The exception is made for zero-day updates which are conducted asap.