Email - Improving Delivery Rates
From All n One's bxp software Wixi
Contents
1 Overview
Email is a global communication solution and has drastically altered how the world works. Like traditional mail it has pros and cons, people who use it for good reasons and those who seek to abuse the system.
Email spam is a global issue. The statistics of sending and receiving spam email boggle the mind. Some companies do nothing but spend all day every day sending spam. There are just as many companies who spend the same amount of time helping to filter out email spam!
Some useful and interesting sites include:
- http://www.spamcop.net/spamstats.shtml
- http://www.trendmicro.com/us/security-intelligence/current-threat-activity/global-spam-map/
Spam may be against the law but the global nature of email makes it very hard to police.
http://en.wikipedia.org/wiki/Email_spam
There are two side of the email coin for any organisation receiving emails and sending valid marketing communications. In order to understand how best to approach the issue you need to know about some of the tools and techniques employed in attempting to stop spam.
2 The Basic Options
There are two types of content for emails. Text and HTML emails. Firstly spam and badness happens in HTML emails. So if you make your emails text only, it improves the delivery rate. It will look a lot visually less appealing.
Do not attach documents. If you need to attach documents, put the document on a publicly accessible website and put a link to the file in the email. This means that email firewalls are more link not to restrict your email for size reasons. Very security concious companies do not allow ANY attachments into the business.
There are many good tips from experienced marketers to help your delivery
- https://econsultancy.com/blog/8054-15-best-practice-tips-for-improving-email-deliverability/
- https://blog.kissmetrics.com/improve-email-deliverability/
- http://www.emailvendorselection.com/email-deliverability-checklist-improve-email-deliverability-now/
3 Basic Email Communication
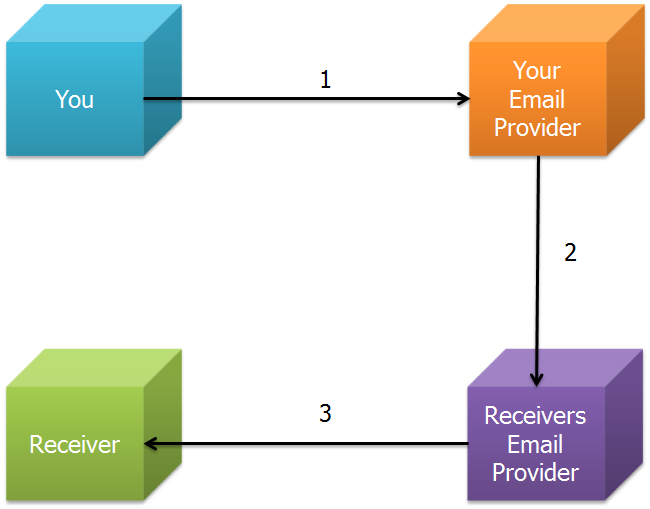
In the simplest terms, email happens in three steps.
- You send an email which you give to your email provider to deliver
- Your email provider works out the receivers email provider and gives it to them to mind
- The receiver will at some point log in and retrieve their emails
An email address is made according to a strict set of rules called RDCs (Request For Comments). http://en.wikipedia.org/wiki/Email_address
Lets work a simple example.
You have outlook on your machine. Your email address is demonstration.account@allnone.ie and you are sending an email to demonstration.user@gmail.com.
As part of step 1, there are usually security steps put in place. For example you need a valid user name and password before your mail server will accept the email for delivery.
So we assume a valid login and the mail is given to your email server. The bit after the @ symbol is how your email provider works out where to send it. The server takes the bit after the @ symbol and looks it up, using something called a DNS lookup (Domain Name Service). It turns the name into a number and then uses this number to get in touch with the other server.
Step 2 now happens. Your mail server gets in touch with the recipients email server. In our example, @allnone.ie gets in touch with @gmail.com. There is a bit of a conversation. @allnone asks, do you have a user called demonstration.user? @gmail will reply yes or no. We are going to assume yes for our example.
Step 3 the recipient, logs in with a valid user name and password and gets your email.
4 My mail doesn't get there
4.1 The major problems
Email was invented in more innocent times. As a result there are major flaws in the design. The major flaws predominantly centre around step 2 and that communication are.
- What happens if the receivers email provider is turned off?
- What happens in the receivers email provider is full and has no more space for new emails?
- What happens if the receivers email provider crashes and deletes all the stored emails before Receiver gets to log in and see the emails.
These are just some minor operational issues but mean that Email is NOT a guaranteed method of communication. Most times its fine... but oh boy when it goes wrong!
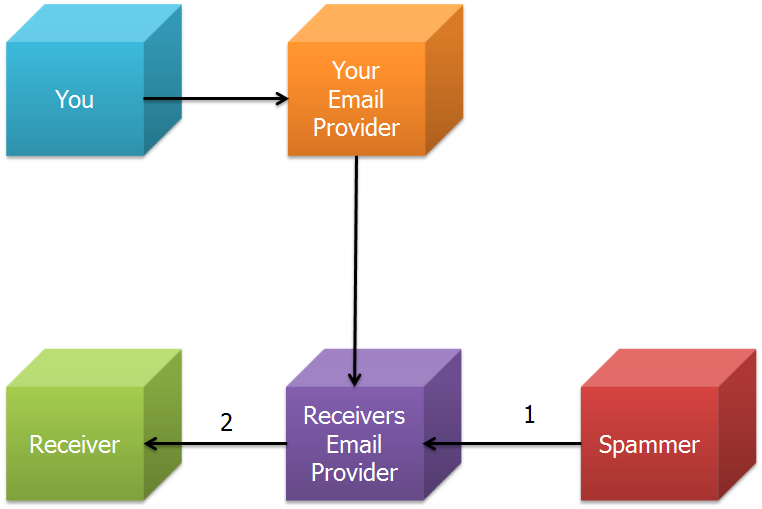
Lets get to the biggest flaw of all. Back in the day, the designers did not see any need for the sending email server to have to validate itself in any way. So the Receivers Email Provider will accept email for demonstration.user@gmail.com from anyone.
There is no way for @gmail.com to reject emails by default. Every email could be valid. So along comes our spammer.
The spammer creates an email and gives it to the Receivers Email Provider. They accept it. Hey Presto! you've got spam.
It is so easy to send spam that you can literally do it from a dos prompt in Windows. Here is a WikiHow, it's that easy!
http://www.wikihow.com/Send-Email-Using-Telnet
4.2 When helpful tools don't help
Even if you do get your email through to your recipient there are a host of reasons why the end user may never see the email. These are totally out of the control of the sender.
- The recipient may have an Outlook rule or similar to delete the email or move it to a subfolder.
- The recipient may have a spam filtering tool installed which didn't like your email for some reason.
- The recipient server may have flagged the email as spam and never allowed the email through
4.3 Checked all of that...
Often the cleanliness of the recipients address, especially in older lists can be called into questions. Companies rebrand and change their address. Some ladies decide to change their surname after getting married and updating of mailbox addresses can be forgotten or not advertised.
Making sure your list is clean and up to date is important when sending as well.
5 Battling spam
Ok, so there are a few different ways to handle spam. None of them are perfect and they all have pros and cons. You need to decide for yourself which you can live with and live without.
Lets have a look at the different stages from our first diagram.
5.1 Stage 1. Sensible user validation
- Require a valid user name
- Require a valid password
- Use encryption on the connection to prevent people intercepting your user name and password
- You could also lock it down such that you can only send email from set IP addresses / location, but that is very restrictive.
- You need to keep your anti-virus, anti-spam and system updates up to date, to prevent people using your machine to send emails without your knowledge.
So this is all hoping that users all keep their systems up to date.
5.2 Stage 1. The message content
- The content of the message can make a huge difference. Text only emails have a much higher delivery percentage.
- Not using attachments, means servers are less likely to refuse the mail on grounds of size
- URLs and Link in the body of the email, get picked up by spam filters
When constructing your emails we have put together a guide with considerations for constructing your emails Writing_HTML_Emails
If you do have to send mass emails, using bxp can reduce the chance of your email account getting blocked for spam, as we have put steps in place to reduced this possibility. Mass_Email_Sending
There are alternatives to attachments. Have a read here to see what alternatives exist Sending_attachments_in_Emails
5.3 Stage 2. Perform a reverse DNS lookup on the sender
So if you really are @allnone.ie, your sending IP address and MX record should be in your DNS record.
This is like not accepting a call from your Mother, unless she is calling from a number you know she will come from. If she rings you from a new land line or a new mobile, you will block the call despite her being genuine, but most of the time it'll be fine.
However, your spammer is unlikely to have hijacked your mothers phone. So you will catch a lot of spammers with this approach.
The massive pitfall is if you don't have your DNS records up to date... a lot of your email will fail.
If you use GMAIL or equivalent to send email, you may not have the IP address available to add to your DNS
If you use a 3rd party company to send marketing emails for you like CakeMail.com, the email will be from their email address not yours!
If you want to use bxp software to do your sending for you, you can add the bxp software IP addresses to your DNS MX records. This can seriously help delivery rates.
Emails from bxp software will come from:
- 82.195.138.167
- 82.195.138.174
So we have them in our DNS records as mail2.allnone.ie and mail3.allnone.ie
This however will only help if the email comes from @allnone.ie. If you need to improve the above you need to add two A records and two MX records to your DNS settings for your domain.
- mail200 14400 IN A 82.195.138.167
- mail300 14400 IN A 82.195.138.174
- yourdomain.com 14400 IN MX 98 mail200.yourdomain.com
- yourdomain.com 14400 IN MX 99 mail300.yourdomain.com
5.4 Stage 2. SpamListing companies
There is a community effort to prevent spamming going on, but not everyone has opted in and there are a number of companies offering service at a number of levels.
When the Receivers Email Provider is contacted it can contact the spam list company and ask "is it ok to accept emails from this IP?" If you are on the black list, the Recievers Email Provider will simply tell the send to go away and fail the email and send back and abrupt "we don't accept from you!" email.
This can be effective BUT it has some massive down falls.
If one of your valid users has become infected or someone is trying to maliciously hit your business, you can get added to a black list very easily. These services are based on automation, user feedback and "likelihood" of being spam. If you get on a black list it can be frustrating, non-centralised and very difficult to get off those lists. Some services are better than others.
One excellent project is http://www.spamhaus.org/ As part of their service they do black listing, but you can pro-actively white list yourself and stop your servers ever getting black listed, IF you are genuine. http://www.spamhauswhitelist.com/en/eligibility.html
5.5 Stage 3. Local spam filtering
"oops" that's ended up in my junk folder. This is a common statement for email users these days. Instead of depending on stages 1, 2 or 3, the user downloads the email and a program installed on the users machine then uses rules to remove the email from the in-box and either delete it immediately or transfer it to a junk folder.
"Delete immediately" is dangerous as the rules can get it wrong and users can lose important emails. The junk folder is safer as at least there is some chance of finding the email. These tools for a corporation are expensive and not 100% reliable as the rules must be constantly revised an updated.
A common and trusted example is http://www.mailwasher.net/
6 Checking for blacklisting
If we are checking for black listing / being listed as a spammer then there are a number of tools we can use.
This meta checking tools, checks numbers of RBL lists to see is the IP blacklisted.
Another useful tool. When you have an IP you want to know more information about, just put it in here.
7 Conclusion
Email sending has devolved into a black art. There are a lot of things you can and can't do. Just chat to us and we'll do what we can to get your delivery rates as high as possible and just make your life simpler!